Table of Contents
Like this article?
Subscribe to our Linkedin Newsletter to receive more educational content
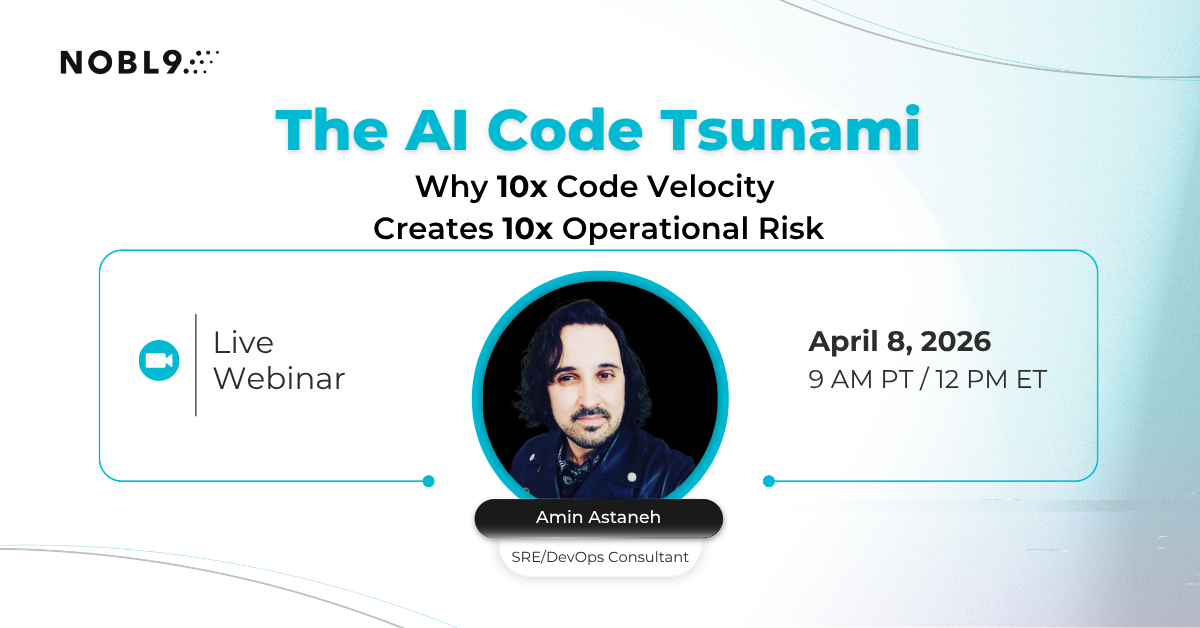
Subscribe nowDevOps teams measure delivery performance through four DORA metrics: deployment frequency, change lead time, change failure rate, and mean time to restore. These metrics quantify CI/CD pipeline maturity and provide benchmarks comparing elite performers (multiple deployments daily with sub-hour recovery time) with low performers (monthly deployments with day-long incident resolution).
Organizations that track DORA metrics gain visibility into their delivery capabilities. Still, raw measurements without a reliability context create perverse incentives that lead teams to optimize for velocity at the expense of user experience.
This article examines how DevOps teams measure performance using deployment frequency, lead time, change failure rate, and recovery metrics, while integrating Error Budget practices to prevent velocity optimization from degrading reliability. We'll cover component-level lead-time analysis to identify actual bottlenecks, SLO-based failure definitions that capture partial degradations missed by binary success/failure tracking, and automated rollback capabilities that reduce recovery time from manual debugging to seconds-scale automated responses.

Customer-Facing Reliability Powered by Service-Level Objectives
Service Availability Powered by Service-Level Objectives
Learn MoreIntegrate with your existing monitoring tools to create simple and composite SLOs
Rely on patented algorithms to calculate accurate and trustworthy SLOs
Fast forward historical data to define accurate SLOs and SLIs in minutes
Summary of key DevOps KPIs and measurement metrics
|
Metric |
What it measures |
How to optimize |
|
Deployment frequency |
How often teams release to production, indicating CI/CD maturity. |
Must be balanced against reliability by tracking rollback frequency and error budget consumption. Progressive delivery and automated rollback enable high velocity while maintaining stability. |
|
Change lead time |
Time from code commit to production deployment across development, review, testing, and deployment stages. |
Requires component-level measurement to identify actual bottlenecks. Testing pipeline optimization and deployment automation reduces lead time without compromising quality. |
|
Change failure rate |
Percentage of deployments causing production incidents. |
Traditional CFR misses partial degradations and performance regressions. SLO-based failure definitions are better suited to measure actual user impact through error budget consumption. |
|
Mean time to restore and recovery |
Recovery speed after incidents |
Suffers from statistical skewing and a reactive nature. The modern approach emphasizes prevention through Error Budget monitoring. Automated rollback triggered by SLO violations reduces recovery time from hours to minutes. |
DORA metrics as a DevOps performance foundation
The DORA (DevOps Research and Assessment) framework provides four standardized metrics that enable consistent performance measurement across teams and organizations. These metrics emerged from multi-year research analyzing thousands of software delivery organizations to identify what separates high performers from low performers.
Core DORA metrics
- Deployment frequency - How often code reaches production
- Lead time for changes - Duration from commit to deployment
- Change failure rate - Percentage of deployments causing incidents
- Time to restore service - Recovery speed after failures
Elite teams demonstrate capabilities that are dramatically different from those of low performers. Teams at the top deploy multiple times daily with lead times under an hour and recovery times measured in minutes.
Low-performing organizations deploy monthly or quarterly, with lead times spanning weeks and recovery taking days. These performance gaps translate directly to business outcomes: faster feature delivery, quicker response to market changes, and reduced time spent firefighting production issues.
The standardization DORA provides matters because it creates a common language for measuring delivery performance. Before DORA, teams tracked deployment success using incompatible definitions where one organization's "deployment" might mean a configuration change while another counted only full application releases. This lack of standardization made meaningful comparisons impossible and prevented organizations from understanding whether their delivery capabilities improved over time.

The four DORA metrics cover deployment frequency, lead time, change failure rate, and time to restore, each with distinct measurement scales that separate elite performers from low performers.
However, raw DORA tracking without a reliability context creates measurement traps. Teams optimize individual metrics through superficial improvements:
- Pushing trivial configuration changes to inflate deployment frequency numbers
- Excluding certain incident types from change failure calculations to improve rates
- Deploying only during low-traffic periods to minimize potential impact.
These gaming behaviors improve metric dashboards without enhancing actual delivery capability or user experience.
Connecting DORA metrics to Service Level Objectives addresses this gaming problem. SLO integration ensures:
- Deployment frequency reflects meaningful releases rather than deployment theatre
- Change failure rates capture actual user impact rather than arbitrary incident classifications
- Recovery metrics measure return to acceptable service levels rather than simply declaring incidents "resolved."
Error budget tracking provides the reliability context needed to prevent velocity optimization from degrading user experience.

Customer-Facing Reliability Powered by Service-Level Objectives
Service Availability Powered by Service-Level Objectives
Learn More
Deployment frequency and velocity optimization
Deployment frequency measures how often teams successfully release changes to production. High deployment frequency reflects mature CI/CD pipelines and comprehensive automated testing. Feature flags play a supporting role here, letting teams ship changes incrementally while keeping production stable.
How deployment frequency impacts delivery capabilities
The relationship between deployment frequency and delivery capability runs deeper than just counting releases. Organizations that deploy multiple times daily have fundamentally different technical and cultural practices than those that deploy monthly. Frequent deployers maintain small batch sizes, with each release containing limited changes. This makes issues easier to identify and roll back more quickly when problems occur.
They have invested in automation that eliminates manual deployment steps prone to human error. They use feature flags to decouple deployment from release, allowing code to reach production in a disabled state before gradual activation.
deployment_maturity = automation_level × batch_size_reduction × risk_mitigation
Progressive delivery techniques enable high deployment frequency while managing risk.
- Canary deployments route small percentages of traffic to new versions while monitoring for issues.
- Blue-green deployments maintain parallel environments for instant rollback.
- Feature flags control functionality exposure independent of deployment timing.
These approaches share a common requirement: real-time monitoring that detects degradations before full rollout.
Error budget-gated deployments prevent gaming behavior in which teams push trivial changes to hit frequency targets. Automated gates pause releases when budget consumption exceeds defined thresholds, signalling that recent deployments have degraded reliability below acceptable levels. This creates natural feedback where deployment velocity automatically adjusts based on quality outcomes rather than arbitrary calendar schedules or sprint boundaries.

The deployment optimization cycle connects auto-scaling configuration, capacity planning, and Error Budget guardrails to maintain reliability while reducing idle capacity.
Infrastructure requirements for sustainable deployment velocity
The automation investment required for high deployment frequency extends beyond CI/CD tooling.
- Comprehensive test automation covering unit, integration, and end-to-end scenarios
- Deployment pipelines with automated rollback triggered by monitoring alerts
- Feature flag infrastructure supporting gradual rollout and instant disable
- Monitoring systems providing real-time feedback on deployment impact
Infrastructure-as-code practices enable consistent environment provisioning and eliminate manual configuration drift. Automated testing frameworks catch regressions before production deployment. Monitoring systems detect degradations during deployment stages rather than waiting for user-reported incidents.
Organizations often struggle to optimize deployment frequency because they treat it as a purely technical problem. The actual constraints frequently involve organizational factors:
- Approval processes requiring manual sign-offs
- Change advisory boards meet weekly to evaluate releases
- Cultural resistance where stability goals conflict with velocity targets.
Technical solutions like automated testing and deployment pipelines only deliver high frequency when organizational practices support rapid, safe releases.
Change lead time and cycle efficiency
Change lead time tracks the duration from code commit to production deployment. This metric reveals where delivery processes accumulate delays and helps teams identify specific bottlenecks requiring different improvement strategies.
Lead time measurement requires breaking the total duration into component stages: coding time, code review, automated testing, manual QA, security review, staging validation, and production deployment. Treating lead time as a single aggregate number obscures where delays actually occur and what interventions might reduce them.
Consider a team with an average lead time of 72 hours. Without stage-level visibility, they might invest in deployment automation, assuming slow deploys cause the problem. Component measurement reveals the actual breakdown: 4 hours coding, 48 hours waiting for code review, 8 hours in automated testing, 4 hours in staging validation, 8 hours waiting for the deployment window. The bottleneck lives in code review capacity, not deployment speed. Automation improvements won't address the actual constraint.
Common lead time bottlenecks and targeted solutions
|
Stage |
Bottleneck Indicators |
Optimization Approaches |
|
Coding |
Extended work-in-progress time |
Requirements clarification, technical debt reduction, pair programming |
|
Code Review |
PRs are waiting days for review |
Reviewer capacity increase, review automation, and smaller batch sizes |
|
Testing |
Slow test execution, flaky tests |
Test parallelization, infrastructure upgrades, and flaky test elimination |
|
Deployment |
Manual steps, scheduling constraints |
Deployment automation, progressive delivery, and elimination of deployment windows elimination |
Long coding times signal different problems than extended review periods.
Development delays
Developers spending days or weeks implementing features may face unclear requirements, significant technical debt requiring refactoring alongside feature work, or architectural complexity making changes difficult. These issues need better requirement specification, dedicated technical debt sprints, or architectural improvements rather than process automation.
Code review delays
Extended code review delays indicate capacity constraints or communication bottlenecks. When PRs routinely wait multiple days for initial review, teams either lack sufficient reviewer capacity or haven't established review expectations. Solutions involve expanding the reviewer pool, setting review time expectations, or implementing automated review for style and simple issues to reduce manual review burden.

Error Budget consumption thresholds determine whether cost-optimization changes proceed automatically, require review, or trigger an immediate rollback.
Testing bottlenecks
Testing bottlenecks come in several forms. Slow test execution (test suites taking hours to complete) requires investment in test infrastructure: more powerful runners, better parallelization, or faster test databases. Flaky tests that pass/fail randomly for identical code waste time investigating false failures and erode confidence in the test suite. Inadequate test coverage forces extensive manual QA before deployment. Each problem needs different fixes: infrastructure upgrades, systematic flaky test elimination, or expanded automated test coverage.
Deployment automation
Deployment automation addresses the final stage but requires careful implementation. GitOps workflows automatically deploy changes when they merge to specific branches, eliminating manual deployment steps and scheduling constraints. Progressive delivery minimizes deployment risk by gradually rolling out with automated monitoring. Automated rollback triggered by SLO violations reduces deployment risk by enabling instant reversion when issues arise.
Lead time optimization
Lead time optimization requires matching interventions to actual constraints. Teams often default to automation investments because technical solutions feel more tractable than organizational changes. However, automating deployment when code review creates the actual bottleneck wastes effort on non-constraining factors. Effective lead time reduction starts with measurement, identifying where time accumulates, and then applying targeted improvements to those specific stages.
Visit SLOcademy, our free SLO learning center
Visit SLOcademy. No Form.Change failure rate and reliability impact measurement
Change failure rate quantifies what percentage of deployments cause production incidents requiring remediation. Traditional CFR divides failed deployments by total deployments, but this simple calculation obscures more than it reveals because "failure" lacks a standardized definition across organizations.
The definition problem manifests in several ways. Some teams consider any deployment requiring a rollback a failure, while others consider only incidents that cause user-visible impact failures. Some organizations exclude planned maintenance deployments from the denominator but include unplanned hotfixes in failure counts. Some teams classify partial degradations (e.g., a 500 error rate increasing from 0.1% to 0.5%) as acceptable rather than failures. These inconsistent definitions make CFR comparisons meaningless and prevent organizations from understanding whether their deployment quality improves over time.
Binary success/failure classification
Binary success/failure classification misses degradations that significantly impact users without triggering traditional incident response. A deployment that increases API latency from 200ms to 800ms might not breach any hard timeout limits or trigger error alerts, but conversion rates drop as users abandon slow-loading pages. A change affecting 2% of users based on specific browser versions or geographic locations might not justify a full rollback, but still degrades the experience for thousands of customers. Traditional CFR treats these scenarios as successful deployments despite measurable user impact.

Example of the Nobl9’s SLO oversight dashboard with the Health widget
SLO-based failure definitions
SLO-based failure definitions provide consistent, user-impact-focused criteria. Instead of subjective assessments about whether a deployment "failed," teams define acceptable service levels through error rate budgets, latency percentiles, and availability targets. Any deployment that consumes error budget beyond the defined thresholds counts as a failure, regardless of whether teams declared an incident or executed a rollback. This approach captures partial degradations, performance regressions, and issues affecting user subsets that binary classifications miss.
Automated deployment validation
deployment_validation_stages:
- canary_deployment: 5% traffic for 15 minutes
- SLO_checks: [error_rate < 0.5%, p95_latency < 500ms]
- rollback_trigger: error_budget_burn_rate > 2x baseline
- staged_rollout: 25% → 50% → 100%
- SLO_monitoring: continuous during each stage
- pause_conditions: budget_consumption > stage_threshold
- post_deployment_validation: 4 hours
- comprehensive_SLO_checks: all service dependencies
- automatic_rollback: budget_depletion_rate_unsustainable
Real-time SLO monitoring during deployment stages detects degradations as they occur rather than waiting for user complaints or manual investigation. Canary deployments route small percentages of traffic to new versions while comparing error rates, latency distributions, and other SLO metrics against baseline measurements. When canary metrics show degradation, automated rollback prevents full deployment.
This approach reduces the blast radius of problematic changes from affecting all users to impacting only the canary traffic percentage.
Error budget tracking
Error budget tracking during deployments provides quantifiable metrics for rollback decisions. Traditional approaches rely on subjective judgment:
- Does this increase in error rate justify a rollback?
- Does this latency regression warrant reverting?
Error budget consumption removes the subjective element. If deployment causes the budget burn rate to exceed sustainable levels, automated rollback executes regardless of whether the absolute error numbers seem "high" or "low" to human observers.

The Nobl9’s Burn Rate threshold configuration mechanism allows fine-tuning levels to meet the organization’s needs.
CFR improvement requires a systematic analysis of failure patterns beyond simply tracking the aggregate percentage. Configuration errors, dependency version conflicts, insufficient capacity allocation, database migration issues, and third-party service degradations each need different prevention strategies.
Teams should categorize failures by root cause and invest in improvements that address the most common patterns: configuration validation automation, dependency testing in staging environments, capacity modeling before deployment, or database migration dry runs. The relationship between CFR and deployment frequency creates interesting dynamics.
Lower CFR doesn't automatically indicate better deployment practices if teams achieve it by deploying less frequently or only during low-traffic periods. High-performing teams often maintain moderate CFR (5-15%) while deploying multiple times daily because they've optimized for fast detection and recovery rather than preventing all failures.
Their deployment processes include automated rollback, comprehensive monitoring, and small batch sizes that limit the impact of failures, making rapid iteration sustainable despite occasional issues.
Learn how 300 surveyed enterprises use SLOs
Download ReportMean time to restore vs. SLO-based recovery
Mean time to restore (MTTR) measures how quickly teams recover service after incidents. Traditional MTTR calculations average resolution time across all incidents, but this statistical approach yields misleading metrics that don't reflect actual recovery capability or user impact.
The averaging problem
The averaging problem emerges when incident distributions skew heavily. Organizations typically experience many minor incidents (configuration problems resolved in minutes, partial service degradations affecting small user percentages) and rare severe outages (database corruption requiring hours of recovery, cascading failures across multiple services). Calculating average MTTR across these diverse incidents produces a number that doesn't accurately represent either scenario.
Example incident distribution over 30 days:
- 45 incidents resolved in < 5 minutes (automated rollback)
- 12 incidents resolved in 15-30 minutes (configuration fixes)
- 2 incidents requiring 4+ hours (database recovery, cascading failures)
Average MTTR: 23 minutes
Median MTTR: 6 minutes
95th percentile MTTR: 180+ minutes
The median MTTR (6 minutes) better reflects typical recovery but understates the impact of severe incidents. The 95th percentile captures worst-case scenarios but ignores that most incidents resolve quickly. Neither single metric adequately describes the organization's recovery capability or user experience during incidents.
Recovery maturity
Recovery maturity varies dramatically based on automation capabilities and architectural choices. Manual debugging approaches require engineers to identify the root cause, develop fixes, test changes, and deploy remediation processes, taking hours or days depending on complexity and time of day (incidents at 3 am face staffing constraints). Automated rollback triggered by SLO violations bypasses the entire debugging process by reverting to the last known good state, reducing recovery time to seconds or minutes regardless of the root cause.
Recovery capability maturity levels:
- Manual investigation - Engineers debug issues, identify causes, and develop fixes (hours to days)
- Runbook automation - Documented procedures execute common remediation steps (30-60 minutes)
- Automated rollback - SLO violations trigger immediate reversion to the previous version (seconds to minutes)
- Self-healing systems - Services automatically detect and remediate common failures without human intervention
Modern reliability approaches shift focus from recovery speed to incident prevention. Mean time between failures (MTBF) measures how often incidents occur rather than how quickly teams resolve them. Error budget tracking shows reliability trends over time and identifies services consuming budget faster than sustainable rates. SLO violation patterns reveal whether incidents result from deployment issues, infrastructure problems, dependency failures, or capacity constraints.
Error budget state determines operational priorities. Teams with healthy error budgets (consuming budget well below the allocated rate) can prioritize feature velocity, experimental deployments, and aggressive optimization efforts. Depleted budgets trigger a focus on reliability:
- Deployment freezes
- Technical debt sprints
- Architecture improvements
- Capacity expansion.
This approach prevents the common pattern where teams optimize MTTR (getting good at recovering from frequent incidents) rather than reducing incident frequency.

Traditional MTTR focuses on speed of resolution, while SLO-based recovery prioritizes user experience impact and proportional resource allocation.
The prevention-focused approach recognizes that even with perfect MTTR, user impact still occurs. An incident resolved in 5 minutes still affects users during that window: failed transactions, abandoned shopping carts, degraded user experience.
Preventing incidents altogether provides better outcomes than recovering from them quickly. Error budget monitoring enables proactive prevention by identifying reliability degradation trends before they become user-visible incidents.
Automated rollback capabilities represent the most significant improvement in recovery for deployment-related incidents. When SLO violations occur during or immediately after deployment, automated systems revert to the previous version without waiting for human investigation or root cause analysis. This approach works because deployment-related incidents have a known remediation (rollback to the previous version) regardless of the specific failure cause, whether a configuration error, code regression, a dependency conflict, or a capacity issue.
Why MTTR is not enough
Traditional MTTR measurement treats all recovery time equally, regardless of incident severity, user impact, or business consequences. A 30-minute recovery from a minor API degradation affecting 5% of request counts is the same as a 30-minute recovery from a complete service outage affecting all users. This equivalence obscures what actually matters: user experience and business impact.
SLO-based reliability measurement addresses these limitations by connecting operational metrics to user experience outcomes. Instead of tracking abstract "incidents" and "recovery time," SLO approaches measure whether services meet defined reliability targets and how much error budget remains for experimentation and velocity optimization.
For a comprehensive exploration of MTTR limitations and SLO-based alternatives, see Is MTTR Dead? Why SLOs Are Revolutionizing Reliability.
Try our SLO Implementation ROI Calculator
Try ROI CalculatorConclusion
DORA metrics provide standardized measurements for deployment frequency, lead time, change failure rate, and recovery time across DevOps teams. Traditional implementation tracks these metrics independently, but modern approaches integrate error budget monitoring to connect delivery velocity with actual user impact. Component-level measurement identifies specific bottlenecks in development, testing, and deployment stages rather than treating lead time as a single number.
Automated SLO monitoring during deployments detects degradations that binary success/failure tracking misses. Progressive delivery techniques like canary deployments and feature flags enable high deployment frequency while automated rollback triggered by SLO violations reduces recovery from manual debugging to seconds-scale responses. Teams balance velocity and reliability by gating deployments on error budget health rather than optimizing individual metrics in isolation.
Navigate Chapters:

-1.png)